Is it possible to add Authorization headers to all outgoing request from colyseus/Client (ts implementation)?
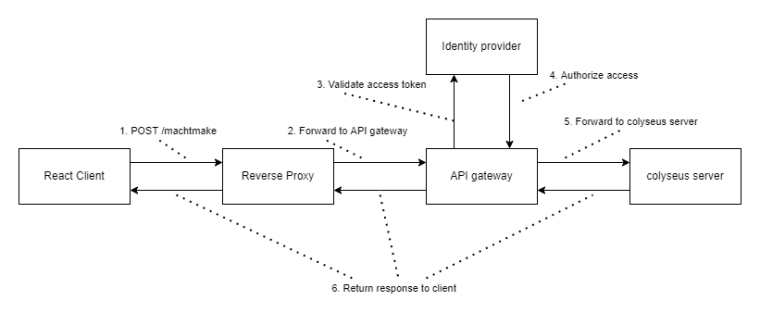
I have an API gateway that's secured through OpenID-Connect and would like to move my colyseus server behind it so I can use the same users as for my other services.
In the official documentation I've only found the possibility to add an accessToken for an FB login on the .login() method but maybe I've missed something.
Specifically I'm wondering about the POST to /matchmake as well as the GET for the session.
Thank you very much for this great tool and your assistance!